It is more faster and easier to pass the CompTIA CAS-003 exam by using Download CompTIA CompTIA Advanced Security Practitioner (CASP) questuins and answers. Immediate access to the Far out CAS-003 Exam and find the same core area CAS-003 questions with professionally verified answers, then PASS your exam with a high score now.
Free CAS-003 Demo Online For CompTIA Certifitcation:
NEW QUESTION 1
After a security incident, an administrator would like to implement policies that would help reduce fraud and the potential for collusion between employees. Which of the following would help meet these goals by having co-workers occasionally audit another worker's position?
- A. Least privilege
- B. Job rotation
- C. Mandatory vacation
- D. Separation of duties
Answer: B
Explanation:
Job rotation can reduce fraud or misuse by preventing an individual from having too much control over an area.
Incorrect Answers:
A: The principle of least privilege prevents employees from accessing levels not required to perform their everyday function.
C: Mandatory vacation is used to discover misuse and allow the organization time to audit a suspected employee while they are away from work.
D: Separation of duties requires more than one person to complete a task. References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, p. 245
NEW QUESTION 2
In a situation where data is to be recovered from an attacker’s location, which of the following are the FIRST things to capture? (Select TWO).
- A. Removable media
- B. Passwords written on scrap paper
- C. Snapshots of data on the monitor
- D. Documents on the printer
- E. Volatile system memory
- F. System hard drive
Answer: CE
Explanation:
An exact copy of the attacker’s system must be captured for further investigation so that the original data can remain unchanged. An analyst will then start the process of capturing data from the most volatile to the least volatile.
The order of volatility from most volatile to least volatile is as follows: Data in RAM, including CPU cache and recently used data and applications Data in RAM, including system and network processes
Swap files (also known as paging files) stored on local disk drives Data stored on local disk drives
Logs stored on remote systems Archive media
Incorrect Answers:
A: Removable media is not regarded as volatile data.
B: Passwords written on scrap paper is not regarded as volatile data. D: Documents on the printer is not regarded as volatile data.
F: Data stored on the system hard drive is lower in the order of volatility compared to system memory.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 250-254
http://blogs.getcertifiedgetahead.com/security-forensic-pHYPERLINK "http://blogs.getcertifiedgetahead.com/security-forensic-performance-basedquestion/" erformaHYPERLINK "http://blogs.getcertifiedgetahead.com/security-forensicperformance- based-question/"nce-based-question/
NEW QUESTION 3
Compliance with company policy requires a quarterly review of firewall rules. A new administrator is asked to conduct this review on the internal firewall sitting between several internal networks. The intent of this firewall is to make traffic more restrictive. Given the following information answer the questions below:
User Subnet: 192.168.1.0/24 Server Subnet: 192.168.2.0/24 Finance Subnet:192.168.3.0/24 Instructions: To perform the necessary tasks, please modify the DST port, Protocol, Action, and/or Rule Order columns. Firewall ACLs are read from the top down
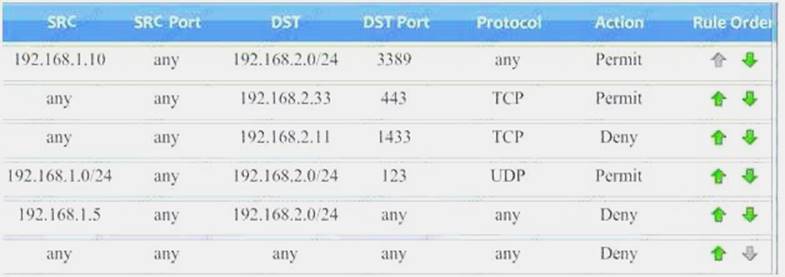
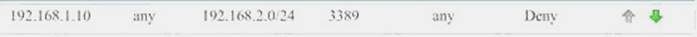
Task 1) An administrator added a rule to allow their machine terminal server access to the server subnet. This rule is not working. Identify the rule and correct this issue.
Task 2) All web servers have been changed to communicate solely over SSL. Modify the appropriate rule to allow communications.
Task 3) An administrator added a rule to block access to the SQL server from anywhere on the network. This rule is not working. Identify and correct this issue.
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.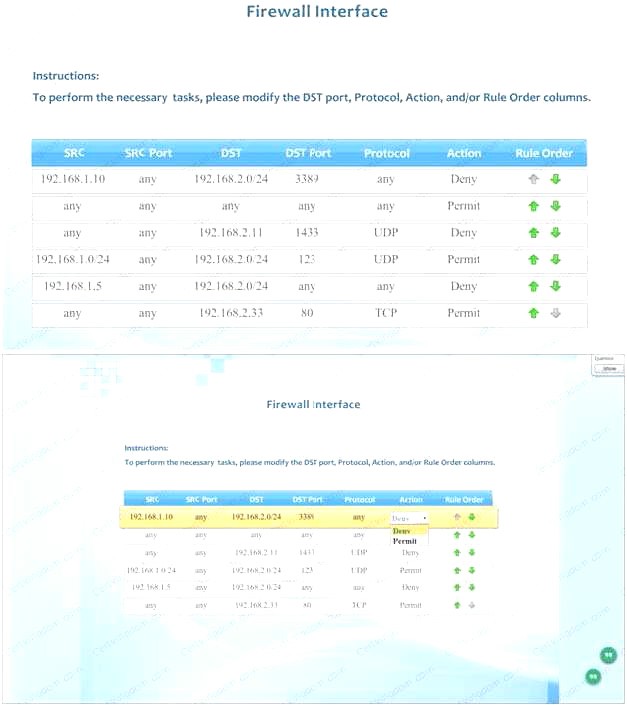
- A. Check the answer below
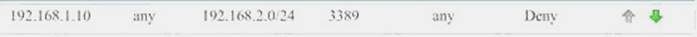
 Task 1) An administrator added a rule to allow their machine terminal server access to the server subne
Task 1) An administrator added a rule to allow their machine terminal server access to the server subne - B. This rule is not workin
- C. Identify the rule and correct this issue.The rule shown in the image below is the rule in questio
- D. It is not working because the action is set to Den
- E. This needs to be set to Permit.
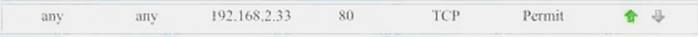
 Task 2) All web servers have been changed to communicate solely over SS
Task 2) All web servers have been changed to communicate solely over SS - F. Modify the appropriate rule to allow communications.The web servers rule is shown in the image belo
- G. Port 80 (HTTP) needs to be changed to port 443 for HTTPS (HTTP over SSL).
 Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ
Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ - H. This rule is not workin
- I. Identify and correct this issue.The SQL Server rule is shown in the image belo
- J. It is not working because the protocol is wron
- K. It should be TCP, not UDP.
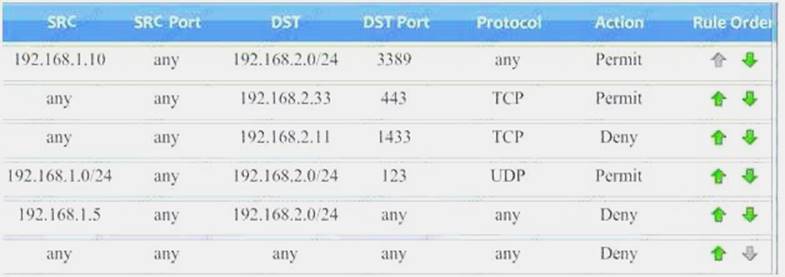
 Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.The network time rule is shown in the image below.
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.The network time rule is shown in the image below.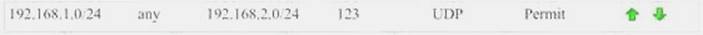 However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul
However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul - L. To block all other traffic, the ‘any’ rule needs to be set to Deny, not Permit and the rule needs to be placed below all the other rules (it needs to be placed atthe bottom of the list to the rule is enumerated last).

- M. Check the answer below
 Task 1) An administrator added a rule to allow their machine terminal server access to the server subne
Task 1) An administrator added a rule to allow their machine terminal server access to the server subne - N. This rule is not workin
- O. Identify the rule and correct this issue.The rule shown in the image below is the rule in questio
- P. It is not working because the action is set to Den
- Q. This needs to be set to Permit.
 Task 2) All web servers have been changed to communicate solely over SS
Task 2) All web servers have been changed to communicate solely over SS - R. Modify the appropriate rule to allow communications.The web servers rule is shown in the image belo
- S. Port 80 (HTTP) needs to be changed to port 443 for HTTPS (HTTP over SSL).Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ
- T. This rule is not workin
- . Identify and correct this issue.The SQL Server rule is shown in the image belo
- . It is not working because the protocol is wron
- . It should be TCP, not UDP.
 Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that noother traffic is allowed.The network time rule is shown in the image below.However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that noother traffic is allowed.The network time rule is shown in the image below.However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul - . To block all other traffic, the ‘any’ rule needs to be set to Deny, not Permit and the rule needs to be placed below all the other rules (it needs to be placed atthe bottom of the list to the rule is enumerated last).

Answer: A
NEW QUESTION 4
After multiple service interruptions caused by an older datacenter design, a company decided to migrate away from its datacenter. The company has successfully completed the migration of all datacenter servers and services to a cloud provider. The migration project includes the following phases:
Selection of a cloud provider Architectural design Microservice segmentation Virtual private cloud Geographic service redundancy Service migration
The Chief Information Security Officer (CISO) is still concerned with the availability requirements of critical company applications. Which of the following should the company implement NEXT?
- A. Multicloud solution
- B. Single-tenancy private cloud
- C. Hybrid cloud solution
- D. Cloud access security broker
Answer: D
NEW QUESTION 5
A Chief Information Security Officer (CISO) has requested that a SIEM solution be implemented. The CISO wants to know upfront what the projected TCO would be before looking further into this concern. Two vendor proposals have been received:
Vendor A: product-based solution which can be purchased by the pharmaceutical company.
Capital expenses to cover central log collectors, correlators, storage and management consoles expected to be $150,000. Operational expenses are expected to be a 0.5 full time employee (FTE) to manage the solution, and 1 full time employee to respond to incidents per year.
Vendor B: managed service-based solution which can be the outsourcer for the pharmaceutical company’s needs.
Bundled offering expected to be $100,000 per year.
Operational expenses for the pharmaceutical company to partner with the vendor are expected to be a 0.5 FTE per year.
Internal employee costs are averaged to be $80,000 per year per FTE. Based on calculating TCO of the two vendor proposals over a 5 year period, which of the following options is MOST accurate?
- A. Based on cost alone, having an outsourced solution appears cheaper.
- B. Based on cost alone, having an outsourced solution appears to be more expensive.
- C. Based on cost alone, both outsourced an in-sourced solutions appear to be the same.
- D. Based on cost alone, having a purchased product solution appears cheape
Answer: A
Explanation:
The costs of making use of an outsources solution will actually be a savings for the company thus the outsourced solution is a cheaper option over a 5 year period because it amounts to 0,5 FTE per year for the company and at present the company expense if $80,000 per year per FTE.
For the company to go alone it will cost $80,000 per annum per FTE = $400,000 over 5 years. With Vendor a $150,000 + $200,000 (½ FTE) = $350,000
With Vendor B = $100,000 it will be more expensive. References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, p. 130
NEW QUESTION 6
During the decommissioning phase of a hardware project, a security administrator is tasked with ensuring no sensitive data is released inadvertently. All paper records are scheduled to be shredded in a crosscut shredded, and the waste will be burned. The system drives and removable media have been removed prior to e-cycling the hardware.
Which of the following would ensure no data is recovered from the system droves once they are disposed of?
- A. Overwriting all HDD blocks with an alternating series of data.
- B. Physically disabling the HDDs by removing the dive head.
- C. Demagnetizing the hard drive using a degausser.
- D. Deleting the UEFI boot loaders from each HD
Answer: C
NEW QUESTION 7
An organization is considering the use of a thin client architecture as it moves to a cloud-hosted environment. A security analyst is asked to provide thoughts on the security advantages of using thin clients and virtual workstations. Which of the following are security advantages of the use of this combination of thin clients and virtual workstations?
- A. Malicious insiders will not have the opportunity to tamper with data at rest and affect the integrity of the system.
- B. Thin client workstations require much less security because they lack storage and peripherals that can be easily compromised, and the virtual workstations are protected in the cloud where security is outsourced.
- C. All thin clients use TPM for core protection, and virtual workstations use vTPM for core protection with both equally ensuring a greater security advantage for a cloud-hosted environment.
- D. Malicious users will have reduced opportunities for data extractions from their physical thin client workstations, this reducing the effectiveness of local attacks.
Answer: B
NEW QUESTION 8
An organization’s network engineering team recently deployed a new software encryption solution
to ensure the confidentiality of data at rest, which was found to add 300ms of latency to data readwrite requests in storage, impacting business operations.
Which of the following alternative approaches would BEST address performance requirements while meeting the intended security objective?
- A. Employ hardware FDE or SED solutions.
- B. Utilize a more efficient cryptographic hash function.
- C. Replace HDDs with SSD arrays.
- D. Use a FIFO pipe a multithreaded software solutio
Answer: A
NEW QUESTION 9
An educational institution would like to make computer labs available to remote students. The labs are used for various IT networking, security, and programming courses. The requirements are: Each lab must be on a separate network segment.
Labs must have access to the Internet, but not other lab networks.
Student devices must have network access, not simple access to hosts on the lab networks. Students must have a private certificate installed before gaining access.
Servers must have a private certificate installed locally to provide assurance to the students. All students must use the same VPN connection profile.
Which of the following components should be used to achieve the design in conjunction with directory services?
- A. L2TP VPN over TLS for remote connectivity, SAML for federated authentication, firewalls between each lab segment
- B. SSL VPN for remote connectivity, directory services groups for each lab group, ACLs on routing equipment
- C. IPSec VPN with mutual authentication for remote connectivity, RADIUS for authentication, ACLs on network equipment
- D. Cloud service remote access tool for remote connectivity, OAuth for authentication, ACL on routing equipment
Answer: C
Explanation:
IPSec VPN with mutual authentication meets the certificates requirements. RADIUS can be used with the directory service for the user authentication.
ACLs (access control lists) are the best solution for restricting access to network hosts. Incorrect Answers:
A: This solution has no provision for restricting access to hosts on the lab networks. B: This solution has no provision for restricting access to hosts on the lab networks. D: This solution has no provision for restricting access to hosts on the lab networks.
NEW QUESTION 10
A technician receives the following security alert from the firewall's automated system: Match_Time: 10/10/16 16:20:43
Serial: 002301028176
Device_name: COMPSEC1 Type: CORRELATION
Scrusex: domain\samjones Scr: 10.50.50.150
Object_name: beacon detection Object_id: 6005
Category: compromised-host Severity: medium
Evidence: host repeatedly visited a dynamic DNS domain (17 time) After reviewing the alert, which of the following is the BEST analysis?
- A. the alert is a false positive because DNS is a normal network function.
- B. this alert indicates a user was attempting to bypass security measures using dynamic DNS.
- C. this alert was generated by the SIEM because the user attempted too many invalid login attempts.
- D. this alert indicates an endpoint may be infected and is potentially contacting a suspect hos
Answer: B
NEW QUESTION 11
A hospital’s security team recently determined its network was breached and patient data was accessed by an external entity. The Chief Information Security Officer (CISO) of the hospital approaches the executive management team with this information, reports the vulnerability that led to the breach has already been remediated, and explains the team is continuing to follow the appropriate incident response plan. The executive team is concerned about the hospital’s brand reputation and asks the CISO when the incident should be disclosed to the affected patients. Which of the following is the MOST appropriate response?
- A. When it is mandated by their legal and regulatory requirements
- B. As soon as possible in the interest of the patients
- C. As soon as the public relations department is ready to be interviewed
- D. When all steps related to the incident response plan are completed
- E. Upon the approval of the Chief Executive Officer (CEO) to release information to the public
Answer: A
NEW QUESTION 12
Which of the following activities is commonly deemed “OUT OF SCOPE” when undertaking a penetration test?
- A. Test password complexity of all login fields and input validation of form fields
- B. Reverse engineering any thick client software that has been provided for the test
- C. Undertaking network-based denial of service attacks in production environment
- D. Attempting to perform blind SQL injection and refilected cross-site scripting attacks
- E. Running a vulnerability scanning tool to assess network and host weaknesses
Answer: C
Explanation:
Penetration testing is done to look at a network in an adversarial fashion with the aim of looking at what an attacker will use. Penetration testing is done without malice and undertaking a networkbased denial of service attack in the production environment is as such ‘OUT OF SCOPE’.
Incorrect Answers:
A: Testing the password complexity of login fields and the input validation of form fields can form part of penetration testing. This is part of the gaining access phase of penetration testing.
B: Making use of reverse engineering a thick client software package would fall within the scope of penetration testing.
D: Blind SQL injection and refilected cross-site scripting attacks can be used in penetration testing. It would form part of the escalation of privilege step in penetration testing.
E: A vulnerability scanning tool to check network and host weakness would be admissible in penetration testing because it is part of the scanning process of penetration testing. References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 91, 166-167
NEW QUESTION 13
An IT manager is concerned about the cost of implementing a web filtering solution in an effort to mitigate the risks associated with malware and resulting data leakage. Given that the ARO is twice per year, the ALE resulting from a data leak is $25,000 and the ALE after implementing the web filter is $15,000. The web filtering solution will cost the organization $10,000 per year. Which of the following values is the single loss expectancy of a data leakage event after implementing the web filtering solution?
- A. $0
- B. $7,500
- C. $10,000
- D. $12,500
- E. $15,000
Answer: B
Explanation:
The annualized loss expectancy (ALE) is the product of the annual rate of occurrence (ARO) and the single loss expectancy (SLE). It is mathematically expressed as: ALE = ARO x SLE
Single Loss Expectancy (SLE) is mathematically expressed as: Asset value (AV) x Exposure Factor (EF) SLE = AV x EF - Thus the Single Loss Expectancy (SLE) = ALE/ARO = $15,000 / 2 = $ 7,500 References:
http://www.financeformulas.net/Return_on_Investment.html https://en.wikipedia.org/wiki/Risk_assessment
NEW QUESTION 14
A security engineer is attempting to increase the randomness of numbers used in key generation in a system. The goal of the effort is to strengthen the keys against predictive analysis attacks.
Which of the following is the BEST solution?
- A. Use an entropy-as-a-service vendor to leverage larger entropy pools.
- B. Loop multiple pseudo-random number generators in a series to produce larger numbers.
- C. Increase key length by two orders of magnitude to detect brute forcing.
- D. Shift key generation algorithms to ECC algorithm
Answer: A
NEW QUESTION 15
A security manager looked at various logs while investigating a recent security breach in the data center from an external source. Each log below was collected from various security devices compiled from a report through the company’s security information and event management server.
Logs: Log 1:
Feb 5 23:55:37.743: %SEC-6-IPACCESSLOGS: list 10 denied 10.2.5.81 3 packets
Log 2: HTTP://www.company.com/index.php?user=aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
Log 3:
Security Error Alert
Event ID 50: The RDP protocol component X.224 detected an error in the protocol stream and has disconnected the client
Log 4:
Encoder oe = new OracleEncoder ();
String query = “Select user_id FROM user_data WHERE user_name = ‘ ”
+ oe.encode ( req.getParameter(“userID”) ) + “ ‘ and user_password = ‘ “
+ oe.encode ( req.getParameter(“pwd”) ) +” ‘ “; Vulnerabilities
Buffer overflow SQL injection ACL
XSS
Which of the following logs and vulnerabilities would MOST likely be related to the security breach? (Select TWO).
- A. Log 1
- B. Log 2
- C. Log 3
- D. Log 4
- E. Buffer overflow
- F. ACL
- G. XSS
- H. SQL injection
Answer: BE
Explanation:
Log 2 indicates that the security breach originated from an external source. And the vulnerability that can be associated with this security breach is a buffer overflow that happened when the amount of data written into the buffer exceeded the limit of that particular buffer.
Incorrect Answers:
A: Log 1 is not indicative of a security breach from an outside source
C: Log 3 will not be displayed if the breach in security came from an outside source. D: Log 4 does not indicate an outside source responsible for the security breach.
F: The access control lists are mainly used to configure firewall rules and is thus not related to the security breach.
G: XSS would be indicative of an application issue and not a security breach that originated from the outside.
H: A SQL Injection is a type of attack that makes use of a series of malicious SQL queries in an attempt to directly manipulates the SQL database. This is not necessarily a security breach that originated from the outside.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 110-112, 151. 153, 162
NEW QUESTION 16
As a security administrator, you are asked to harden a server running Red Hat Enterprise Server 5.5 64-bit.
This server is being used as a DNS and time server. It is not used as a database, web server, or print server. There are no wireless connections to the server, and it does not need to print.
The command window will be provided along with root access. You are connected via a secure shell with root access.
You may query help for a list of commands. Instructions:
You need to disable and turn off unrelated services and processes.
It is possible to simulate a crash of your server session. The simulation can be reset, but the server cannot be rebooted. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

- A. In Order to deactivate web services, database services and print service, we can do following things1) deactivate its services/etc/init.d/apache2 stop/etc/init.d/mysqld stop2) close ports for these services Web Serveriptables -I INPUT -p tcp -m tcp --dport 443 -j REJECTservice iptables save Print Serveriptables -I INPUT -p tcp -m tcp --dport 631 -j REJECTservice iptables save Database Serveriptables -I INPUT -p tcp -m tcp --dport <<port umber>> -j REJECTservice iptables save3) Kill the process any running for the same ps -aef|grep mysqlkill -9 <<process id>>
- B. In Order to deactivate web services, database services and print service, we can do following things1) deactivate its services/etc/init.d/apache2 stop/etc/init.d/mysqld stop2) close ports for these services Web Serveriptables -I INPUT -p tcp -m tcp --dport <<port umber>> -j REJECTservice iptables save3) Kill the process any running for the same ps -aef|grep mysqlkill -9 <<process id>>
Answer: A
NEW QUESTION 17
Given the following output from a local PC:
Which of the following ACLs on a stateful host-based firewall would allow the PC to serve an intranet website?
- A. Allow 172.30.0.28:80 -> ANY
- B. Allow 172.30.0.28:80 -> 172.30.0.0/16
- C. Allow 172.30.0.28:80 -> 172.30.0.28:443
- D. Allow 172.30.0.28:80 -> 172.30.0.28:53
Answer: B
NEW QUESTION 18
One of the objectives of a bank is to instill a security awareness culture. Which of the following are techniques that could help to achieve this? (Choose two.)
- A. Blue teaming
- B. Phishing simulations
- C. Lunch-and-learn
- D. Random audits
- E. Continuous monitoring
- F. Separation of duties
Answer: BE
NEW QUESTION 19
A government organization operates and maintains several ICS environments. The categorization of one of the ICS environments led to a moderate baseline. The organization has complied a set of applicable security controls based on this categorization.
Given that this is a unique environment, which of the following should the organization do NEXT to determine if other security controls should be considered?
- A. Check for any relevant or required overlays.
- B. Review enhancements within the current control set.
- C. Modify to a high-baseline set of controls.
- D. Perform continuous monitorin
Answer: C
NEW QUESTION 20
......
Thanks for reading the newest CAS-003 exam dumps! We recommend you to try the PREMIUM Certleader CAS-003 dumps in VCE and PDF here: https://www.certleader.com/CAS-003-dumps.html (555 Q&As Dumps)