Passleader 156-215.77 Questions are updated and all 156-215.77 answers are verified by experts. Once you have completely prepared with our 156-215.77 exam prep kits you will be ready for the real 156-215.77 exam without a problem. We have Up to the minute Check-Point 156-215.77 dumps study guide. PASSED 156-215.77 First attempt! Here What I Did.
Online Check-Point 156-215.77 free dumps demo Below:
NEW QUESTION 1
Which of the following firewall modes DOES NOT allow for Identity Awareness to be deployed?
- A. Bridge
- B. Load Sharing
- C. High Availability
- D. Fail Open
Answer: A
NEW QUESTION 2
Which R77 GUI would you use to see the number of packets accepted since the last policy install?
- A. SmartView Monitor
- B. SmartView Tracker
- C. SmartDashboard
- D. SmartView Status
Answer: A
NEW QUESTION 3
SmartView Tracker logs the following Security Administrator activities, EXCEPT:
- A. Object creation, deletion, and editing
- B. Tracking SLA compliance
- C. Administrator login and logout
- D. Rule Base changes
Answer: B
NEW QUESTION 4
The SIC certificate is stored in the directory .
- A. $CPDIR/registry
- B. $CPDIR/conf
- C. $FWDIR/database
- D. $FWDIR/conf
Answer: B
NEW QUESTION 5
Message digests use which of the following?
- A. DES and RC4
- B. IDEA and RC4
- C. SSL and MD4
- D. SHA-1 and MD5
Answer: D
NEW QUESTION 6
What information is found in the SmartView Tracker Management log?
- A. Creation of an administrator using cpconfig
- B. GAiA expert login event
- C. FTP username authentication failure
- D. Administrator SmartDashboard logout event
Answer: D
NEW QUESTION 7
How do you configure the Security Policy to provide user access to the Captive Portal through an external (Internet) interface?
- A. Change the gateway settings to allow Captive Portal access via an external interface.
- B. No action is necessar
- C. This access is available by default.
- D. Change the Identity Awareness settings under Global Properties to allow Captive Portal access on all interfaces.
- E. Change the Identity Awareness settings under Global Properties to allow Captive Portal access for an external interface.
Answer: A
NEW QUESTION 8
To qualify as an Identity Awareness enabled rule, which column MAY include an Access Role?
- A. Action
- B. Source
- C. User
- D. Track
Answer: B
NEW QUESTION 9
Because of pre-existing design constraints, you set up manual NAT rules for your HTTP server. However, your FTP server and SMTP server are both using automatic NAT rules. All traffic from your FTP and SMTP servers are passing through the Security Gateway without a problem, but traffic from the Web server is dropped on rule 0 because of anti- spoofing settings.
What is causing this?
- A. Manual NAT rules are not configured correctly.
- B. Allow bi-directional NAT is not checked in Global Properties.
- C. Routing is not configured correctly.
- D. Translate destination on client side is not checked in Global Properties under Manual NAT Rules.
Answer: D
NEW QUESTION 10
An Administrator without access to SmartDashboard installed a new IPSO-based R77 Security Gateway over the weekend. He e-mailed you the SIC activation key and the IP
address of the Security Gateway. You want to confirm communication between the Security Gateway and the Management Server by installing the Policy. What might prevent you from installing the Policy?
- A. An intermediate local Security Gateway does not allow a policy install through it to the remote new Security Gateway applianc
- B. Resolve by running the command fw unloadlocal on the local Security Gateway.
- C. You first need to run the command fw unloadlocal on the R77 Security Gateway appliance in order to remove the restrictive default policy.
- D. You first need to create a new Gateway object in SmartDashboard, establish SIC via the Communication button, and define the Gateway’s topology.
- E. You have not established Secure Internal Communications (SIC) between the Security Gateway and Management Serve
- F. You must initialize SIC on the Security Management Server.
Answer: C
NEW QUESTION 11
What happens if the identity of a user is known?
- A. If the user credentials do not match an Access Role, the system displays the Captive Portal.
- B. If the user credentials do not match an Access Role, the system displays a sandbox.
- C. If the user credentials do not match an Access Role, the traffic is automatically dropped.
- D. If the user credentials match an Access Role, the rule is applied and traffic is accepted or dropped based on the defined action.
Answer: D
NEW QUESTION 12
Study the Rule base and Client Authentication Action properties screen -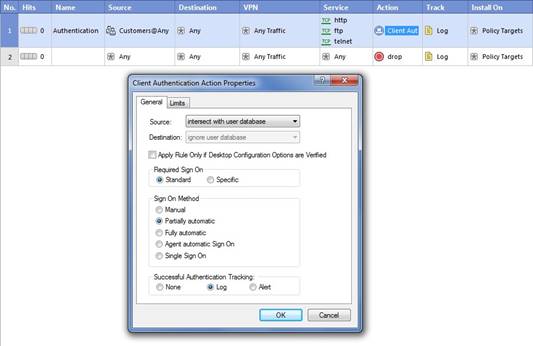
After being authenticated by the Security Gateway, when a user starts an HTTP connection to a Web site, the user tries to FTP to another site using the command line. What happens to the user?
- A. user is prompted for authentication by the Security Gateway again.
- B. FTP data connection is dropped after the user is authenticated successfully.
- C. user is prompted to authenticate from that FTP site only, and does not need to enter his username and password for Client Authentication.
- D. FTP connection is dropped by Rule 2.
Answer: C
Explanation:
Manual Users must use either telnet to port 259 on the firewall, or use a Web browser to connect to port 900 on the firewall to authenticate before being granted access.
# Partially Automatic If user authentication is configured for the service the user is attempting to access and they pass this authentication, then no further client authentication is required. For example, if HTTP is permitted on a client authentication rule, the user will be able to transparently authenticate since FireWall-1 has a security server for HTTP.Then, if
this setting is chosen, users will not have to manually authenticate for this connection. Note that this applies to all services for which FireWall-1 has built-in security servers (HTTP, FTP, telnet, and rlogin).
# Fully Automatic If the client has the session authentication agent installed, then no further client authentication is required (see session
authentication below). For HTTP, FTP, telnet, or rlogin, the firewall will authenticate via user authentication, and then session authentication will be used to authenticate all other services.
http://www.syngress.com
Figure 6.19 Client Authentication Action Properties 278 Chapter 6 • Authenticating Users
# Agent Automatic Sign On Uses session authentication agent to provide transparent authentication (see session authentication below).
# Single Sign-On System Used in conjunction with UserAuthority servers to provide enhanced application level security. Discussion of UserAuthority is beyond the scope of this book.
NEW QUESTION 13
Central license management allows a Security Administrator to perform which of the following functions?
1. Check for expired licenses.
2. Sort licenses and view license properties.
3. Attach both R77 Central and Local licesnes to a remote module.
4. Delete both R77 Local Licenses and Central licenses from a remote module.
5. Add or remove a license to or from the license repository.
6. Attach and/or delete only R77 Central licenses to a remote module (not Local licenses).
- A. 1, 2, 5, & 6
- B. 2, 3, 4, & 5
- C. 2, 5, & 6
- D. 1, 2, 3, 4, & 5
Answer: D
NEW QUESTION 14
Which SmartConsole component can Administrators use to track changes to the Rule Base?
- A. WebUI
- B. SmartView Tracker
- C. SmartView Monitor
- D. SmartReporter
Answer: B
NEW QUESTION 15
Certificates for Security Gateways are created during a simple initialization from ____.
- A. sysconfig
- B. The ICA management tool
- C. SmartUpdate
- D. SmartDashboard
Answer: D
NEW QUESTION 16
......
P.S. Certshared now are offering 100% pass ensure 156-215.77 dumps! All 156-215.77 exam questions have been updated with correct answers: https://www.certshared.com/exam/156-215.77/ (388 New Questions)