Actualtests N10-008 Questions are updated and all N10-008 answers are verified by experts. Once you have completely prepared with our N10-008 exam prep kits you will be ready for the real N10-008 exam without a problem. We have Improve CompTIA N10-008 dumps study guide. PASSED N10-008 First attempt! Here What I Did.
Free demo questions for CompTIA N10-008 Exam Dumps Below:
NEW QUESTION 1
An administrator would like to allow Windows clients from outside me office to access workstations without using third-party software. Which or the following access methods would meet this requirement?
- A. Remote desktop gateway
- B. Spit tunnel
- C. Site-to-site VPN
- D. VNC
Answer: A
Explanation:
To allow Windows clients from outside the office to access workstations without using third-party software, the administrator can use the Remote Desktop Protocol (RDP). RDP is a built-in feature of the Windows operating system that allows users to remotely connect to and control other Windows computers over a network connection.
To use RDP, the administrator will need to enable the Remote Desktop feature on the workstations that need to be accessed, and ensure that the appropriate firewall rules are in place to allow RDP traffic to pass through. The administrator will also need to provide the remote users with the necessary credentials to access the workstations.
Once RDP is set up and configured, the remote users can use the Remote Desktop client on their own computers to connect to the workstations and access them as if they were physically present in the office. This allows the administrator to provide remote access to the workstations without the need for any additional software or third-party tools.
NEW QUESTION 2
A company is being acquired by a large corporation. As part of the acquisition process, the
company's address should now redirect clients to the corporate organization page. Which of the following DNS records needs to be created?
- A. SOA
- B. NS
- C. CNAME
- D. TXT
Answer: C
Explanation:
Reference: https://www.namecheap.com/support/knowledgebase/article.aspx/9604/2237/types-of-domain-redirects-301-302-url-redirects-url-frame-and-cname/#:~:text=CNAME%20record%20is%20actually%20not,often%20mistakenly%20used%20as%20such.&text=In%20other%20words%2C%20CNAME%20record,address%20of%20the%20destination%20hostname CNAME (Canonical Name) is a type of DNS record that maps an alias name to another name, which can be either another alias or the canonical name of a host or domain. A CNAME record can be used to redirect clients from one domain name to another domain name, such as from the company’s address to the corporate organization page. SOA (Start of Authority) is a type of DNS record that specifies authoritative information about a DNS zone, such as the primary name server, contact email address, serial number, refresh interval, etc., which does not redirect clients to another domain name. NS (Name Server) is a type of DNS record that specifies which name server is authoritative for a domain or subdomain, which does not redirect clients to another domain name. TXT (Text) is a type of DNS record that provides arbitrary text information about a domain or subdomain, such as SPF (Sender Policy Framework) records or DKIM (DomainKeys Identified Mail) records, which does not redirect clients to another domain name.
NEW QUESTION 3
A network technician was troubleshooting an issue for a user who was being directed to cloned websites that were stealing credentials. The URLs were correct for the websites but an incorrect IP address was revealed when the technician used ping on the user's PC After checking the is setting, the technician found the DNS server address was incorrect Which of the following describes the issue?
- A. Rogue DHCP server
- B. Misconfigured HSRP
- C. DNS poisoning
- D. Exhausted IP scope
Answer: C
Explanation:
DNS poisoning is a type of attack that modifies the DNS records of a domain name to point to a malicious IP address instead of the legitimate one. This can result in users being directed to cloned websites that are stealing credentials, even if they enter the correct URL for the website. The incorrect DNS server address on the user’s PC could be a sign of DNS poisoning, as the attacker could have compromised the DNS server or spoofed its response to redirect the user’s queries. References: https://www.comptia.org/blog/what-is-dns-poisoning
NEW QUESTION 4
The results of a recently completed site survey indicate a significant, undesired RSSI in the parking lot and other exterior areas near the like to mitigate access to the wireless network in exterior access areas. The current access point settings are listed in the following table: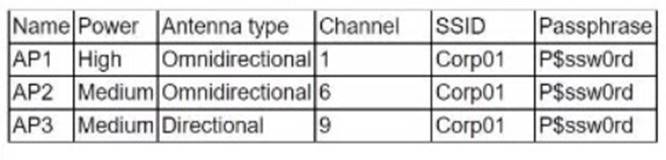
Which of the following is the BEST step for the technician to take to resolve the issue?
- A. Reconfigure AP2 and AP3 for non-overlapping channels
- B. Implement directional antennas on AP1 and AP2.
- C. Raise the power settings on AP2 and AP3.
- D. Change the SSID on AP1 and AP2.
Answer: B
Explanation:
Implementing directional antennas on AP1 and AP2 is the best step for the technician to take to resolve the issue of undesired RSSI in the parking lot and other exterior areas near the building. RSSI stands for received signal strength indicator, which is a measure of how well a device can receive a wireless signal from an access point (AP). An AP is a device that provides wireless connectivity to a network. An antenna is a device that radiates or receives electromagnetic waves. A directional antenna is an antenna that focuses the wireless signal in a specific direction, resulting in higher gain and longer range. By using directional antennas on AP1 and AP2, which are located near the exterior walls of the building, the technician can reduce the wireless signal leakage to the outside areas and improve the wireless coverage inside the building. References: [CompTIA Network+ Certification Exam Objectives], What Is RSSI and How Does It Affect Wireless Networks?, Directional Antennas: Everything You Need to Know
NEW QUESTION 5
In which of the following components do routing protocols belong in a software-defined network?
- A. Infrastructure layer
- B. Control layer
- C. Application layer
- D. Management plane
Answer: B
Explanation:
A software-defined network (SDN) is a network architecture that decouples the control plane from the data plane and centralizes the network intelligence in a software controller. The control plane is the part of the network that makes decisions about how to route traffic, while the data plane is the part of the network that forwards traffic based on the control plane’s instructions. The control layer is the layer in an SDN that contains the controller and the routing protocols that communicate with the network devices. The control layer is responsible for managing and configuring the network devices and providing them with the necessary information to forward traffic. References: https://www.comptia.org/training/books/network-n10-008-study-guide (page 378)
NEW QUESTION 6
A network administrator is trying to create a subnet, which is the most efficient size possible, for 31 laptops. Which of the following network subnets would be best in this situation?
- A. 10.10.10.0/24
- B. 10.10.10.0/25
- C. 10.10.10.0/26
- D. 10.10.10.0/27
Answer: D
Explanation:
A /27 subnet mask has 32 IP addresses, of which 30 are usable for hosts. This is the smallest subnet that can accommodate 31 laptops, as the other options have either too few or too many IP addresses. A /27 subnet mask is equivalent to 255.255.255.224 in decimal notation, and has a wildcard mask of 0.0.0.31. The network address is 10.10.10.0, and the broadcast address is 10.10.10.31. The usable host range is 10.10.10.1 to 10.10.10.30.
References
1: Subnet Cheat Sheet – 24 Subnet Mask, 30, 26, 27, 29, and other IP Address CIDR Network References
2: IP Subnet Calculator
NEW QUESTION 7
Which of the following protocols would enable a company to upgrade its internet connection by acquiring its own public IP prefixes and autonomous system number?
- A. EIGRP
- B. BGP
- C. IPv6
- D. MPLS
Answer: B
Explanation:
BGP is a routing protocol that is used to exchange routing information between different autonomous systems (ASes) on the internet. An autonomous system is a network or group of networks that is under the same administrative control and uses a common routing protocol. By acquiring its own public IP prefixes and autonomous system number, a company can use BGP to advertise these prefixes to other ASes and establish its own internet connection. This would enable the company to have more control over its internet connection and potentially improve its connectivity.EIGRP (Enhanced Interior Gateway Routing Protocol) is a routing protocol used within a single autonomous system, so it would not be used to establish a connection to the internet. IPv6 is a version of the Internet Protocol (IP) used to identify devices on a network. It is not a routing protocol and would not be used to establish an internet connection.MPLS (Multi-Protocol Label Switching) is a networking technology that is used to route packets between different networks. It is not a routing protocol and would not be used to establish an internet connection.
NEW QUESTION 8
A network administrator is configuring logging on an edge switch. The requirements are to log each time a switch port goes up or down. Which of the following logging levels will provide this information?
- A. Warnings
- B. Notifications
- C. Alert
- D. Errors
Answer: B
Explanation:
Notifications are the lowest logging level and will provide the desired information regarding switch port up/down activity. According to the CompTIA Network+ Study Manual, notifications "are used for logging normal activities, such as port up/down events, link changes, and link flaps."
NEW QUESTION 9
A network administrator is troubleshooting a client's device that cannot connect to the network. A physical inspection of the switch shows the RJ45 is connected. The NIC shows no activity lights. The network administrator moves the device to another location and connects to the network without issues. Which Of the following tools would be the BEST option for the network administrator to use to further troubleshoot?
- A. Tone generator
- B. Multimeter
- C. Optical time-domain reflectometer
- D. Cable tester
Answer: D
Explanation:
A cable tester is a tool that can verify the integrity and functionality of a network cable. It can measure the electrical characteristics of the cable, such as resistance, capacitance, and impedance, and detect any faults or defects, such as shorts, opens, or crosstalk. A cable tester can help the network administrator troubleshoot the problem by determining if the cable is faulty or not. A tone generator is a tool that can send an audible signal through a cable to help locate and identify it. A multimeter is a tool that can measure voltage, current, and resistance of electrical circuits. An optical time-domain reflectometer (OTDR) is a tool that can test the quality and length of fiber optic cables.
References: CompTIA Network+ Certification Exam Objectives Version 7.0 (N10-007), Objective 2.3: Given a scenario, use the appropriate tool to support wired or wireless networks.
NEW QUESTION 10
While using a secure conference call connection over a corporate VPN, a user moves from a cellular connection to a hotel wireless network. Although the wireless connection and the VPN show a connected status, no network connectivity is present. Which of the following is the most likely cause of this issue?
- A. MAC filtering is configured on the wireless connection.
- B. The VPN and the WLAN connection have an encryption protocol mismatch.
- C. The WLAN is using a captive portal that requires further authentication.
- D. Wireless client isolation is enforced on the WLAN settings.
Answer: C
Explanation:
A captive portal is a web page that is displayed to newly connected users of a Wi-Fi network before they are granted broader access to network resources. Captive portals are commonly used to present a landing or log-in page which may require authentication, payment, acceptance of an end-user license agreement, acceptable use policy, survey completion, or other valid credentials that both the host and user agree to adhere by123
A possible cause of the issue is that the user has not completed the captive portal authentication process, which prevents the VPN from establishing a secure connection over the Wi-Fi network. The user may need to open a web browser and follow the instructions on the captive portal page to gain full access to the internet.
NEW QUESTION 11
A network administrator is given the network 80.87.78.0/26 for specific device assignments. Which of the following describes this network?
- A. 80.87.78 0 - 80.87.78.14
- B. 80.87.78 0 - 80.87.78.110
- C. 80.87.78 1 - 80.87.78.62
- D. 80.87.78.1 - 80.87.78.158
Answer: C
Explanation:
The network 80.87.78.0/26 is a Class A network with a subnet mask of /26, which means that it contains 26 bits of network information and 6 bits of host information.
The range of valid host addresses for this network is 80.87.78.1 to 80.87.78.62. Any addresses outside of this range are reserved for special purposes or are not used.
NEW QUESTION 12
Which of the following is the best action to take before sending a network router to be recycled as electronic waste?
- A. Turn on port security.
- B. Shred the switch hard drive.
- C. Back up and erase the configuration.
- D. Remove the company asset ID tag.
Answer: C
Explanation:
Before disposing of a network router, it is important to back up and erase the configuration to prevent unauthorized access to sensitive data and network settings. A network router may contain information such as passwords, IP addresses, firewall rules, VPN settings, and other network parameters that could be exploited by hackers or malicious users. By backing up the configuration, you can preserve the network settings for future reference or reuse. By erasing the configuration, you can wipe out the data and restore the router to its factory default state.
NEW QUESTION 13
A network administrator wants to improve the security of the management console on the company's switches and ensure configuration changes made can be correlated to the administrator who conformed them Which of the following should the network administrator implement?
- A. Port security
- B. Local authentication
- C. TACACS+
- D. Access control list
Answer: C
Explanation:
TACACS+ is a protocol that provides centralized authentication, authorization, and accounting (AAA) for network devices and users. TACACS+ can help improve the security of the management console on the company’s switches by verifying the identity and credentials of the administrators, enforcing granular access policies and permissions, and logging the configuration changes made by each administrator. This way, the network administrator can ensure only authorized and authenticated users can access and modify the switch settings, and also track and correlate the changes made by each user. References: https://www.comptia.org/blog/what-is-tacacs
NEW QUESTION 14
A technician is troubleshooting reports that a networked printer is unavailable. The printer's IP address is configured with a DHCP reservation, but the address cannot be pinged from the print server in the same subnet. Which of the following is MOST likely the cause of me connectivity failure?
- A. Incorrect VLAN
- B. DNS failure
- C. DHCP scope exhaustion
- D. Incorrect gateway
Answer: D
NEW QUESTION 15
Which of the following types of devices can provide content filtering and threat protection,
and manage multiple IPSec site-to-site connections?
- A. Layer 3 switch
- B. VPN headend
- C. Next-generation firewall
- D. Proxy server
- E. Intrusion prevention
Answer: C
Explanation:
Next-generation firewalls can provide content filtering and threat protection, and can manage multiple IPSec site-to-site connections. References: CompTIA Network+ Certification Study Guide, Chapter 5: Network Security.
NEW QUESTION 16
Which of the following combinations of single cables and transceivers will allow a server to have 40GB of network throughput? (Select two).
- A. SFP+
- B. SFP
- C. QSFP+
- D. Multimode
- E. Cat 6a
- F. Cat5e
Answer: CD
Explanation:
QSFP+ is a type of transceiver that supports 40 gigabit Ethernet (40GbE) over four lanes of 10 gigabit Ethernet (10GbE) each. QSFP+ stands for quad small form-factor pluggable plus, and it is a compact and hot-swappable module that plugs into a QSFP+ port on a network device. QSFP+ transceivers can support various types of cables and connectors, such as direct attach copper (DAC), active optical cable (AOC), or fiber optic cable. Multimode is a type of fiber optic cable that supports multiple modes of light propagation within the core. Multimode fiber optic cable can carry higher bandwidth and data rates than single-mode fiber optic cable, but over shorter distances. Multimode fiber optic cable is commonly used for short-reach applications, such as within a data center or a campus network. Multimode fiber optic cable can be paired with QSFP+ transceivers to achieve 40GbE connectivity.
The other options are not correct because they do not support 40GbE. They are:
✑ SFP+. SFP+ is a type of transceiver that supports 10 gigabit Ethernet (10GbE) over a single lane. SFP+ stands for small form-factor pluggable plus, and it is a compact and hot-swappable module that plugs into an SFP+ port on a network device. SFP+ transceivers can support various types of cables and connectors, such as direct attach copper (DAC), active optical cable (AOC), or fiber optic cable. However, SFP+ transceivers cannot support 40GbE by themselves, unless they are used in a breakout configuration with a QSFP+ transceiver.
✑ SFP. SFP is a type of transceiver that supports 1 gigabit Ethernet (1GbE) over a single lane. SFP stands for small form-factor pluggable, and it is a compact and hot-swappable module that plugs into an SFP port on a network device. SFP transceivers can support various types of cables and connectors, such as twisted- pair copper, coaxial cable, or fiber optic cable. However, SFP transceivers cannot
support 40GbE by themselves, unless they are used in a breakout configuration with a QSFP+ transceiver.
✑ Cat 6a. Cat 6a is a type of twisted-pair copper cable that supports 10 gigabit
Ethernet (10GbE) over distances up to 100 meters. Cat 6a stands for category 6 augmented, and it is an enhanced version of Cat 6 cable that offers better performance and reduced crosstalk. Cat 6a cable can be paired with 10Gbase-T transceivers to achieve 10GbE connectivity. However, Cat 6a cable cannot support 40GbE by itself, unless it is used in a breakout configuration with a QSFP+ transceiver.
✑ Cat 5e. Cat 5e is a type of twisted-pair copper cable that supports 1 gigabit
Ethernet (1GbE) over distances up to 100 meters. Cat 5e stands for category 5 enhanced, and it is an improved version of Cat 5 cable that offers better performance and reduced crosstalk. Cat 5e cable can be paired with 1000base-T transceivers to achieve 1GbE connectivity. However, Cat 5e cable cannot support 40GbE by itself, unless it is used in a breakout configuration with a QSFP+ transceiver.
References1: QSFP+ - an overview | ScienceDirect Topics2: Multimode Fiber - an overview | ScienceDirect Topics3: Network+ (Plus) Certification | CompTIA IT Certifications4: SFP+ - an overview | ScienceDirect Topics5: SFP - an overview | ScienceDirect Topics6: Cat 6a - an overview | ScienceDirect Topics7: [Cat 5e - an overview | ScienceDirect Topics]
NEW QUESTION 17
......
100% Valid and Newest Version N10-008 Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/N10-008-dumps.html (New 514 Q&As)